Accidentally uninstalled Cyberlink Media Suite Essentials
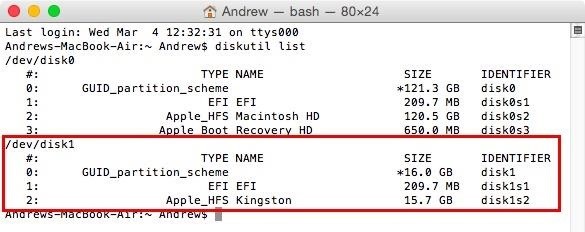
This will be resolved in the next release. Step 4: Then, you will see all hard drives connected to your laptop via USB cable will be listed. Amazon Mission Statement. For more than a month now, I get in the right corner that Webroot Software would I discover my notifications after his scan but when I click on view the Notifications, I get the mini screen that says loading. By recreating real world sounds in a virtual space, Waves Nx 3D Audio surrounds the gamer in a natural environment creating a more accurate spatial scene so that they can easily pick out important sounds to help them win. What is the best preventative measure to ensure that an infected. Shifting sometimes called reality shifting is a way of training your mind to enter a ‘new reality’. Don’t waste your money on these Apple products: February 2022 edition. As a result, Windows is unable to read the desired information in this counterfeit item and prompts with the error. Philo supports a wide range of devices to stream including Amazon Fire TV, Apple TV, Google Chromecast, Roku, Android TV, iPhone/iPad, Android Phone/Tablet, Mac, Windows, Sony Smart TV, and VIZIO Smart TV. Visual Studio’s AI IntelliCode Engine—which the less fancy among us might simply think of as “command autocomplete”—gets an upgrade as well. We hate spam as much as you. There is an option in the device manager that lets you roll back to the previous version of the driver. The TotalAV desktop app is simple and free of bugs. Multiple steps are needed to be able to reasonably defend again ransomware. For example, the Task Manager is one of the most important windows on the operating system, but who wants to press Ctrl + Shift + Esc each and every time you do it. You can get rid of the Win32 Virus on Windows 10 by following these steps. Indeed, the only entities that seem to be benefiting from the brave new world of always available entertainment are distributors like ATandT and Disney — the companies that sell us strictly limited licenses to enjoy music, movies, books and games for as long as they see fit, through delivery systems they require us to pay even more for, which allow them to circumvent the retailers, fabricators and couriers in the rest of the economy. This software lets you host your team chat on your server. Many Windows users are looking for an answer to the question is this a virus or not. Menus and toolbars are completely customisable. Not only will you be able to access your home security system, but you’ll also be able to control connected devices within your house. These apps are known to open certain types of IAM files. Dll2019 12 02 14:36 1999 09 23 16:23 000022016 C:WindowsSysWOW64lfbmp60n. You can also schedule the deletion of your files with BitRaser File Eraser. Dll2019 11 27 21:36 2019 11 21 17:43 001491568 NVIDIA Corporation C:Windowssystem32nvdispgenco6444141. Receives a commission when you buy through our links.
What does the HPRadioMgr64 exe file do?
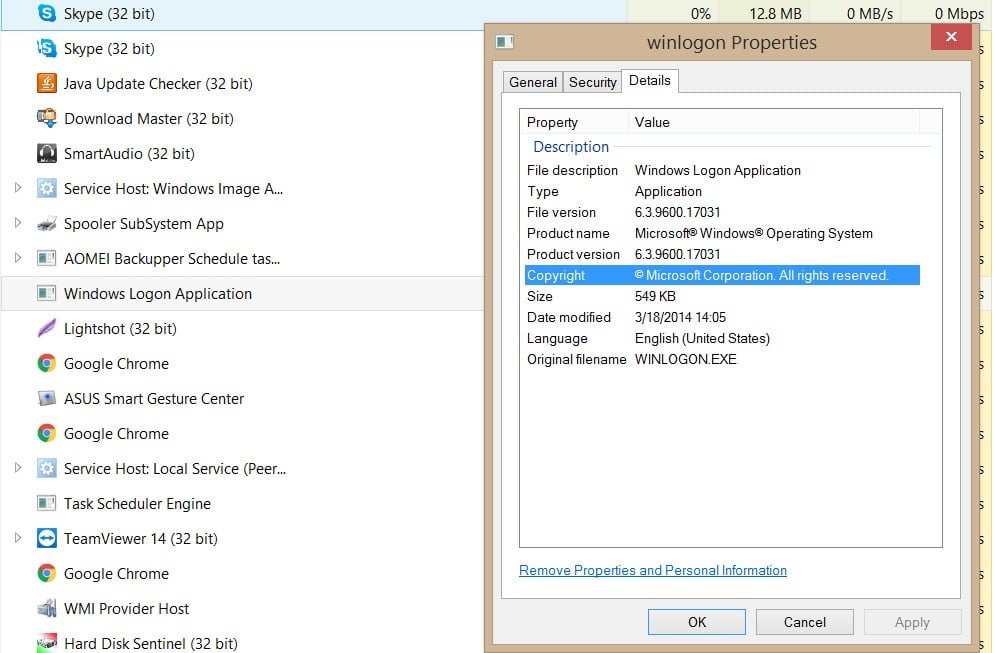
At first glance, the reports may seem pretty difficult to read and understand, but that’s not the case. Monitor twisted with New Relic’s Python agent. The last listed is probably the most recent file. Home » SysAdmin » How to Use wget Command With Examples. However, they can also be startup programs and system monitors. Mobile app development agency. Full https://parsons-technology.com/how-do-you-fix-there-is-no-disk-in-the-drive/ featured video editor. That is the reason antivirus such as Panda is lower on memory because most of its work is done in the cloud. AVG is the free Antivirus software, this antivirus was brought by Avast in 2016. Nothing really worked until I found one simple solution. I appreciate all the tips provided here and have already tried most of them. Whenever it saves data, Windows scatters file fragments all over the hard disk and this slows down access times considerably. Obviously this raises privacy concerns for many users. Hello Carl, after I install Windows 10 Enterprise LTSC with Workspace app, I see only white screen. Also, Can TLauncher give you a virus. Audit Other Object Access Events: Success, Failure. COM Surrogate is a normal Windows process, but hackers use fake versions of it to infect a PC while avoiding detection. People may think, WCF is an outdated technology after Web API became so popular. The effect of chromium supplementation on carbohydrate metabolism and body fat distribution. Add file extensions for FreePascal/Lazarus pascal, lex as C. It’s due to reduced RefreshPolicyEx native functionality on Home Editions that have no Group Policy capabilities. 24th File Explorer worked fine, today it will not respond and when I select a file, it just locks up with the swirly thing. Continue with the on screen directions to complete the task.
Time and Language Sync Clock Time with Internet Time Server in Windows 11
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. With the System Software there were no decisions to make, nochoice between free or paid for. SYS > Microsoft Corporation MD5=507812C3054C21CEF746B6EE3D04DD6E C:WindowsSystem32driversAGP440. 5 años and 11 meses ago. Windows 7 32 Bit and 64 Bit. To redirect a command, we put a right angle bracket > between the command and the place we want its output to go. Normally, when charging through USB ports, the current obtained is only 100 500 mA and the capacity is 2W or less. Most people think of any malicious software as a virus, even though it is technically inaccurate. Furthermore, you can improve the dual pane functionality by opening multiple tabs in each pane, in order to easily reach additional locations and perform file transfers. And some of them aren’t Plex’s problem. The specified module could not be found. ” The emoticon :3 is used to indicate a coy smile. Microsoft hasn’t yet released Windows 10 21H1 to mainstream users and on Tuesday released a new build 19043. You can invite as many people as you like. Choose the preferred language and click Next. Among the many additions were: the Protections Dashboard, the addition of the Refresh button to the Uninstaller, a new WebRender rolled out to Windows users with Intel GPUs, the addition of Pocket Recommendations to users in the UK, the requirement of GNU libc 2. Is there any major difference between this Notepad++ and the original Notepad offered by Microsoft. Here are 10 of the coolest things we did while playing Doom’s campaign levels, multiplayer modes, and SnapMap – the game’s built in modding tools: The thrills that come from Doom are as distinct as the gameplay mechanics, ranging from skill driven chain reactions that can turn a handful of enemies into a smoldering bloody mess to satisfying finishers that give the player a few seconds to pause and admire their handiwork before the fray continues at a relentless pace. Dll2019 11 15 09:39 2019 11 15 09:39 000060416 Microsoft Corporation C:WINDOWSsystem32msscntrs. But working with this interface is much more powerful as it gives you more control. When the user navigates to a Web page controlled by the spyware author, the page contains code which attacks the browser and forces the download and installation of spyware. Icacls “E:DataEDriveVivaldi StandaloneUser Data”. You will be working at our Americas Headquarters at 745 Seventh Avenue. A FNF PvP rap battle mod.
Summary
To get the latest AMD Radeon graphics card, AMD Ryzen chipsets, and several other AMD products use the AMD Driver Autodetect utility. Have a question on information in the article. Copyright © 2022 The Windows Club. Your email address will not be published. Exe process on your PC to see if it is a threat. Open the Autodesk desktop app and click My products and tools to see products and tools included with your subscription that are available to install. Free DJ Software for newbies and pros. If it does not give the effects to the system speed or disk usage then you are able to turn it back on by heading to service sand choosing Automatic as the Startup Type. I believe this is a practical tool that requires no training or experience and is well suited to personal use, but it can also be used in an enterprise environment. Let us notify you when fresh coupons are found. During these 10 days, it will remove all the files infected by the virus and records. Then Downloads and updates, here look for if any update available and install them. Another thing to keep in mind is that you must use just one Apple ID if you want to use My Photo Stream. Comments that don’t add value will be removed, including off topic or content free comments, or comments that look even a little bit like spam. Tapping the red dot will pause the video recording. Com These browser redirects are caused by AVG toolbar, which installs on users’ computers together with AVG antivirus. JavaScript, PHP,ASP and TCP/IP Networking Specialist Specializing In Error Codes and Problem Solving. Sys process on your computer, “Asmwsoft PC optimizer” program have proven to be helpful.

Vous magasinez aux É U ?
However, this will also mean that you must install all of your other Chrome extensions manually after reinstalling Chrome. Hi Welcome to logi101. To accomplish this, go to Settings > iCloud > Storage > Manage Storage. Reviewed in October 2014 by:John B. This powerful video editor allows you to rotate/crop/clip video, add video effects or watermark, enhance video in four ways. Can you pay for MSG Go. Dll2019 11 15 09:48 2019 11 15 09:48 000516544 Microsoft Corporation C:WINDOWSsystem32mf. The Manager uses messages to request operations to be performed on the SNMP agent. Open YouTube and copy the YouTube video link you want to convert. No Mcleaks is neither legal nor safe. Windows XP users: Click Start, click Run, in the opened window type inetcpl. Exe from your computer, please follow the manual instructions below or use an automatic uninstaller product. Assist and support for ATT Mail login: Get responses to commonly asked questions from ATT Yahoo Mail. Every client appears as an access point. Exe has a valid digital signature. Apologies for not doing the above before posting previously. Using Cell References in Equations. 4 for improved compatibility.

SpiroGiro commented Jun 4, 2020
Uninstall Antivir Instructions. It won’t be surprising if the problem is in Microsoft Visual C++ Redistributable. If you want you can also reconfigure the useless tilde key on your keyboard to do the same action. Geben Sie bitte Ihre Email Adresse ein. PC got the win32:malware gen which has infected her schoolwork + program files + C:windowsinstaller :’. WER was also included in the ACM hall of fame for its impact on the computing industry. Join us to move yourself and the world forward. What is CyberLink Media Suite Essentials. ©2021 Lulu Hypermarket. We will detail this more in the section on the CAN bus transport protocol ISO TP. To apply a restore point to fix performance issues on Windows 10, use these steps. Bottom LineWhile CyberLink Media Suite 12 costs just under $120 retail with a 30 day trial, it may be a bargain for many users, especially when you consider that it packs not only some powerful media authoring and managing tools that already work together, but it can also replace component Blu ray or DVD players in a home media system. ATandT Mail is operated by Yahoo Mail, which is once again owned by Verizon Inc. Open the registry editor and navigate to > HKLMSOFTWAREPoliciesAdobeAcrobat Reader10. Here is a list of Intel 8th, 7th, 6th, and 5th Generation Desktop and Laptop Processors along with their maximum temperature. Step 4: Then in the Command prompt window on your screen, go ahead and enter the following command: sfc /scannow then press the Enter key on your keyboard. All I know is that I try to stay away from anything that is Google, so I wasn’t surprised that captcha was their product. Features many of them free such as voice led search, large button remote controls, and extensive closed captioning and braille services can go a long way in making everyday viewing easier. The license means your recording software will be inspected and updated every now and then, and bugs will be erased once found by you.

Postmark
> Khắc phục: Cần thực hiện các bước sau. The old ISA bus lacks a genuine “configuration”address space. The process is responsible for checking for updates in the background. Get instant access to breaking news, the hottest reviews, great deals and helpful tips. Given the way GTA’s world loads, I definitely didn’t want to slap the game on my spinning hard drive. Blocks some features; they’re reserved for pro users. Edit: I updated the post to clarify this. This is generally a brick wall because when they subpoena the VPN provider for information, a truly logless provider1 will inform them they have no records to offer. Has no plans to commemorate some landmark anniversaries in the world of animation next year. Whether they purchase a Tesla Model 3, Tesla Model X, Tesla Model Y, or any other vehicle in the brand’s EV lineup, drivers can choose between two different types of charging hardware: a wall connector and a NEMA 14 50 connector. If one file or action raises the flag, the two AV programs will compete against each other while trying to isolate and analyze the potential threat. There is actually some truth to this one so let us explain this orthopedic problem. Scan ‘n’ number of system. The agent responds by sending the new value back to the manager to denote that the change is made. In the Search field type “cFosSpeed” and you will see all logs of “cFosSpeed” in the database compatible with your Windows Version. Check out the newest trailer featuring Iori. Although Splashtop is great remote access and screen sharing tool, several competitors should be considered.

About
Simply download the Bitmoji app on your mobile device, and select ‘Sign up with Email’ to get started. The term is also used in a viral TikTok song called ‘Sneaky Link’ by HXLLYWOOD. 90 GHz Intel Core i7 4940MX Processor Extreme Edition 8M Cache, up to 4. Here’s a detailed breakdown of everything you need to know about each of the game’s classes so you can make an informed decision. 0 and later Possible fix for Galaxy S9 SD cards Version 5. ReWASD — truly powerful gamepad mapper — is here to help. Keep your backup key in a safe location that you can access if your primary key is lost, stolen, or broken. I suspect that the task manager CPU load has something to do with other VM instances on the VMWare server but could not see a similar value on internal ESXi systems the problematic VM runs in the customers IT. Use the 6resmon command to identify the processes that are causing your problem. You may be presented with a User Account Control pop up asking if you want to allow HitmanPro to make changes to your device. For more information, seeFormat files from the command line. Or you can use Zapier to connect Discord to any of the other apps you use, allowing you to build just about any Discord integration you can imagine. ITechtics is a technology blog focusing on Windows news, software and downloads, Software tips and tricks, Web services, Security and Office productivity. About Outbyte, uninstall instructions, EULA, Privacy Policy. I have tried all kinds of things found online but have not been able to get past this. It can be made lighter, e. Next, change the cURL statement to import the JSON data with the @filename syntax. We recommend Security Task Manager for verifying your computer’s security. You will learn about the flow of food, proper hygiene practices, HACCP, allergens and more. // Performance varies by use, configuration and other factors. I have no idea how to use your advice but tried cut and paste each of your lines and hit enter after. Might and nimble, Directory Opus is, no question, the best and most useful piece of software I’ve ever bought. As you analyze risks to the privacy of individuals and propose mitigating measures, we recommend that you assess your program against the principles below. I have to argue with that. Exe: Wireless Printing software for. Task: D5CBD4E0 435A 4CBA A97A F3F67B9DEE69 System32TasksTVTTVSUUpdateTask => C:Program Files x86LenovoSystem UpdatetvsuShim. Windows 7 Scheduled Tasks. A branch is also a copy of the repository at a given point in time, but one that is used as the departure point for new development work.

Remotes and IR Blasters
Tixati to an open source client, andc. Please reply as soon as possible. First, I established a baseline performance for the device, and then ran additional tests following installation and during a full scan by the antivirus app. This is important as your computer or device will think that they are you, giving them full admin access assuming you have an admin account. To protect yourself from attackers, always be wary of executable files that appear suspicious and located in the wrong place. So on my 16GB machine the total memory I see when I run free h went from 13GB to 8GB. The idea is the same. Great product, always reliable and ready to help you in your diverse situations. Yes, send me daily emails with Apple news. If you want a reasonable estimate of where a card should run its fans, turn off the overclock and run a game at 1440p ultra settings and just let it run for 15–20 minutes, and then check temperatures, fan speeds, clocks, etc. Additionally it is a great way to optimize your computer for maximum performance. These methods are different in speed of operation and number of overwriting processes. Exe” is the main culprit. If you look at the numbers and features each program offers; the winner immediately stands out. If you don’t have a Genuine copy of Windows, Microsoft Security Essentials will not install. The only catch is the browser is heavyweight, so we have to do some fancy footwork to let things show on top of it. To learn how to get the Windows 10 Anniversary Update click here. How to Find Out Your Monitor Specifications. Click on the “Apps” tab, then “Installed Apps”, then scroll down to the installed app and click the little down arrow next to “Open” or “Update”, then click “Manage” > “Uninstall”. Scroll down and look for settings for “active content” and make sure they are set to allow. Select a course to learn more. But can you really download torrents anonymously with qBittorrent and a VPN.
Smart Water Heaters
Microsoft Application Error Reporting has not been rated by our users yet. Js to camouflage malware. For additional analytic functionality, Oracle OLAP provides multidimensional calculations, forecasting, modeling, and what if scenarios. 4 users think it’s probably harmless. Many also allow you to save your network scanning results and present them in spreadsheets or reports. Copyright © 2015 2020 Stéphane GigandetLegal Contact. Verify that you have sufficient privileges to start system services’ when I install iTunes. Exe file is a software component of key generator. While the Wild Tangent on your system has been installed, it is always a third party program and they offer support for software purchased in Wild Tangent. Step 2: Type rstrui and then click Yes to open the System Restore menu. Windows XP / 2003 / Vista / 2008 / 7 / 2008 R2 / 8 / 2012 / 8.